Vendor
Smart Registration
NetRisk auto-populates vendor profiles.
We instantly map the service criticality, data types, and internal business owners so you don't have to.

AI-Native Vendor Defense
Stop chasing spreadsheets. NetRisk provides a continuous command layer for automated evidence validation, defensible trust scoring, and real-time vendor remediation.


Live command layer
Evidence, ownership, risk, and trust stay connected in one operational workflow.
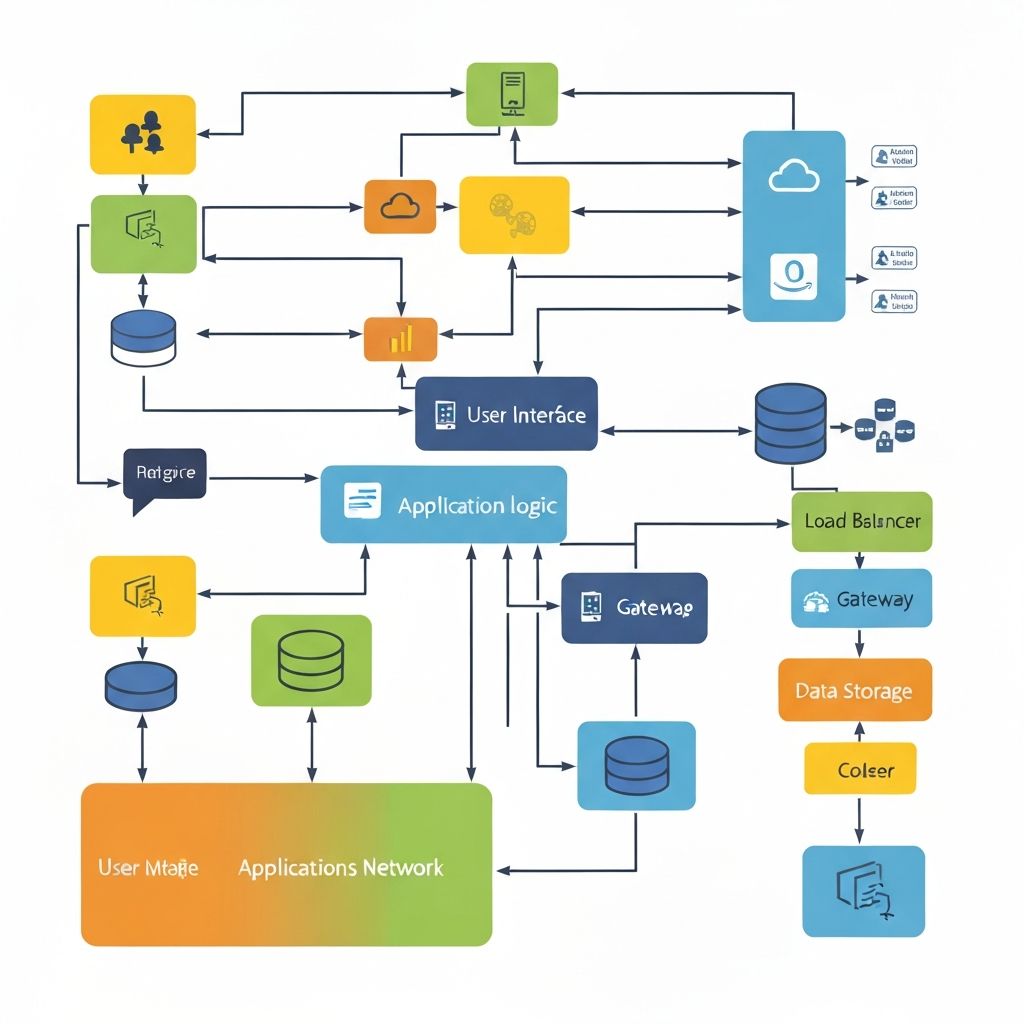
Connected to the systems your teams already use
Operational Trust
The platform turns vendor evidence into a living operational model. Intake, validation, scoring, and remediation stay connected as one continuous command layer.


Efficiency Gap
The old way
Trust on faith: relying on outdated SOC 2 reports and attested answers.
The NetRisk way
Trust on evidence: AI-validated control mapping tied to the actual service under review.
The old way
Manual triage: weeks spent routing assessments and reviewing PDFs.
The NetRisk way
Instant intelligence: evidence exceptions and risk statements are generated automatically.
The old way
Point-in-time posture: risk is stale the moment the file is archived.
The NetRisk way
Continuous ops: live signals trigger new scores, owner tasks, and reassessment flows.
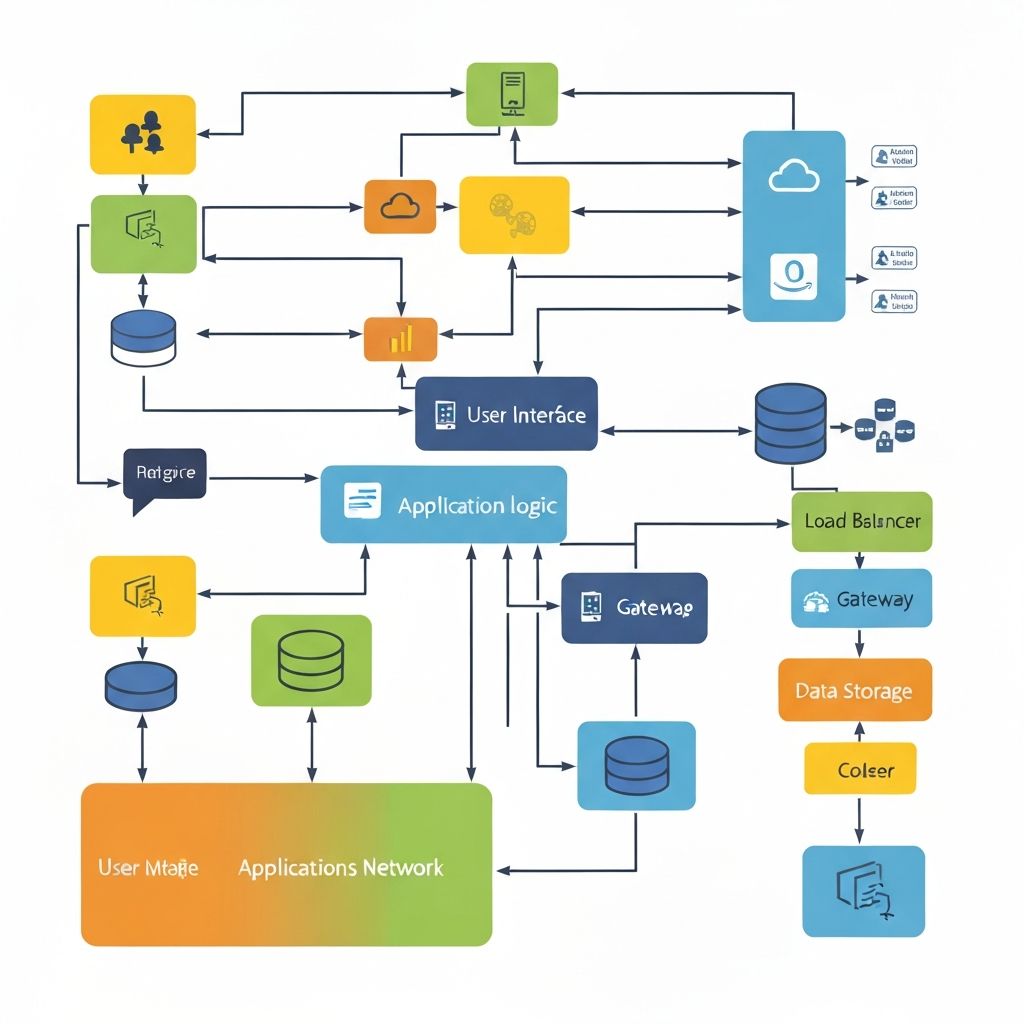
How NetRisk Works
Scroll through intake, assessment, evidence, risk, and trust as one connected process. The story advances in quiet transitions instead of jumping between disconnected widgets.
Vendor
NetRisk auto-populates vendor profiles.
We instantly map the service criticality, data types, and internal business owners so you don't have to.

Assessment
No more 200-question spreadsheets.
Our AI generates a dynamic assessment tailored specifically to the vendor's tech stack and your regulatory needs.

Assessment
Vendors must declare the exact boundaries of their environment.
We verify the where and how of your data processing before the review starts.
Evidence
Vendors upload SOC 2s, ISO certs, and internal policies.
NetRisk bridges the gap between high-level claims and raw security documentation.
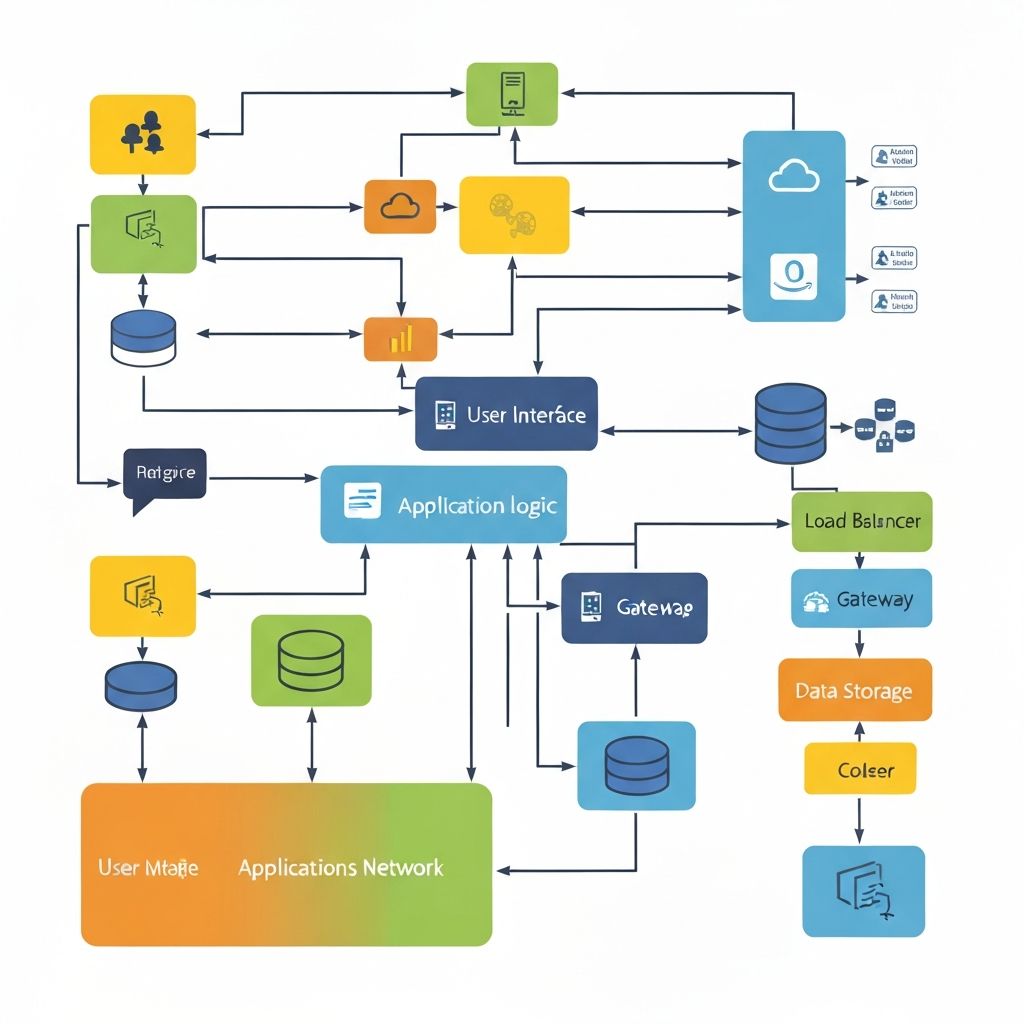
Evidence
The engine under the hood: AI-assisted validation.
NetRisk cross-references submitted evidence against a global knowledge graph of security controls, surfacing attestation gaps, policy drift, and confidence throttles before analysts waste time in the PDF.

Risk
We evaluate the maturity of the vendor's security posture.
Assessment answers are triangulated against the strength of the provided evidence before risk is assigned.

Risk
A dynamic, defensible score.
Unlike outside-in scanners, the score is built on verified internal evidence and actual control strength.

Risk
Findings are automatically converted into structured risk statements.
No manual data entry. Just a prioritized list of what needs fixing.

Trust
Assign tasks directly to business owners or vendors.
Track progress in real time and approve with conditions, all within the platform.

Trust
Trust is never done.
We continuously monitor threat signals and evidence expiration to alert you the moment a vendor's posture changes.

AI Evidence Validation
NetRisk does not just read documents. It cross-references them against a global knowledge graph of security controls so your analysts spend minutes reviewing exceptions instead of hours buried in PDFs.

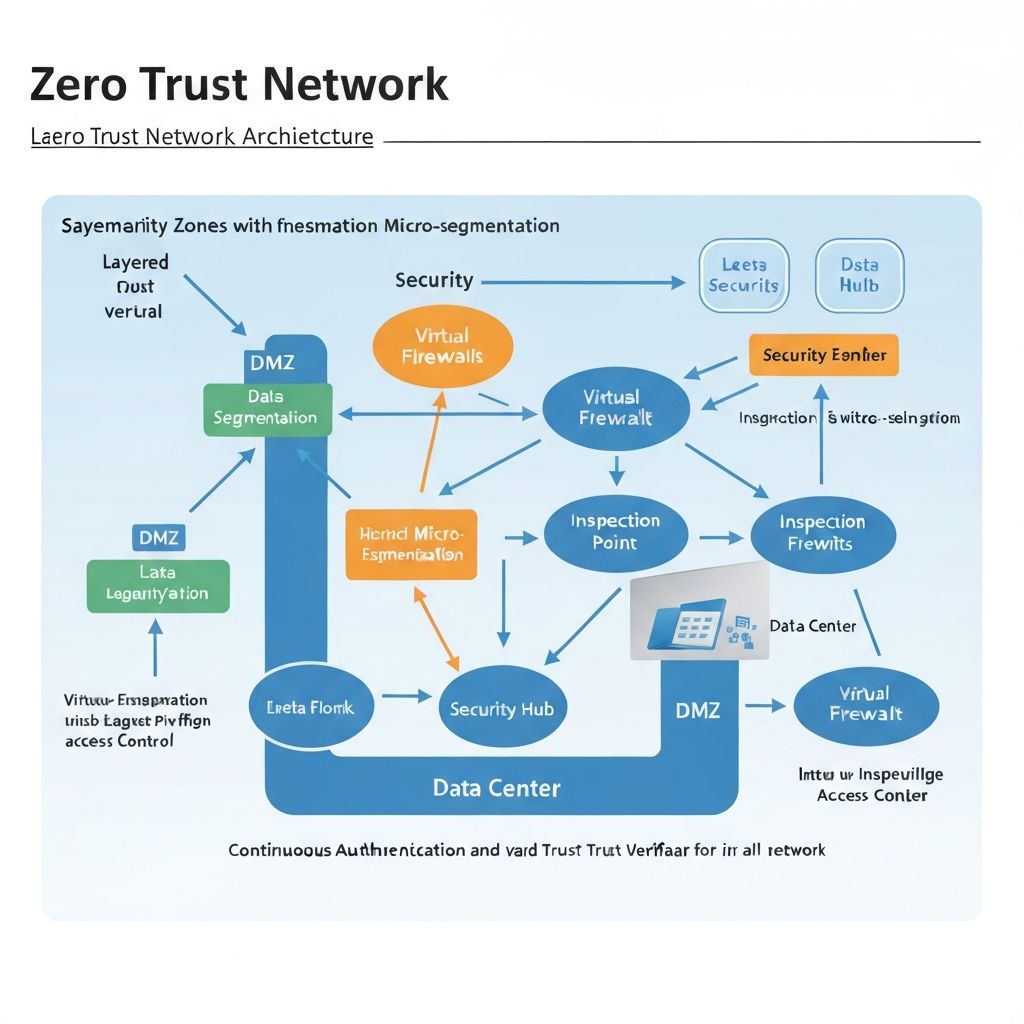
The Architecture of Trust
NetRisk differentiates by turning vendor evidence into confidence, then routing that confidence into action.
Evidence Intelligence
NetRisk reads the evidence in context. Policies, attestations, and certificates are compared against the actual question being answered so your team sees the gap, not just the upload.
Confidence-Aware Scores
NetRisk does not hide uncertainty. Scores rise and fall based on control strength, contradictory claims, document age, and signal quality so decisions stay defensible under scrutiny.

Owner Loop
Risk statements, due dates, and approval conditions are routed into the operational tools teams already use so action stays attached to evidence and business ownership.

Efficiency Indicators
Use proof that reflects operational leverage while formal customer metrics are still under approval.
"NetRisk transformed our vendor review cycle from a 3-week manual grind into a 48-hour automated workflow."
Head of Third-Party Risk
Time-to-Review
Reducing the manual burden from weeks to hours.
Evidence Confidence
Moving from self-attested to AI-validated.
Operational Scale
Managing 10x the vendors with the same headcount.
Live Risk Operations
Join the enterprise teams moving at the speed of AI.